But details in use, when information is in memory and becoming operated on, has normally been more challenging to protected. Confidential computing addresses this significant gap—what Bhatia phone calls the “lacking 3rd leg in the 3-legged knowledge security stool”—via a components-centered root of belief. DOE’s testbeds may also be bein
 Jonathan Lipnicki Then & Now!
Jonathan Lipnicki Then & Now! Andrea Barber Then & Now!
Andrea Barber Then & Now!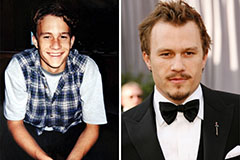 Heath Ledger Then & Now!
Heath Ledger Then & Now! Mary Beth McDonough Then & Now!
Mary Beth McDonough Then & Now! Teri Hatcher Then & Now!
Teri Hatcher Then & Now!